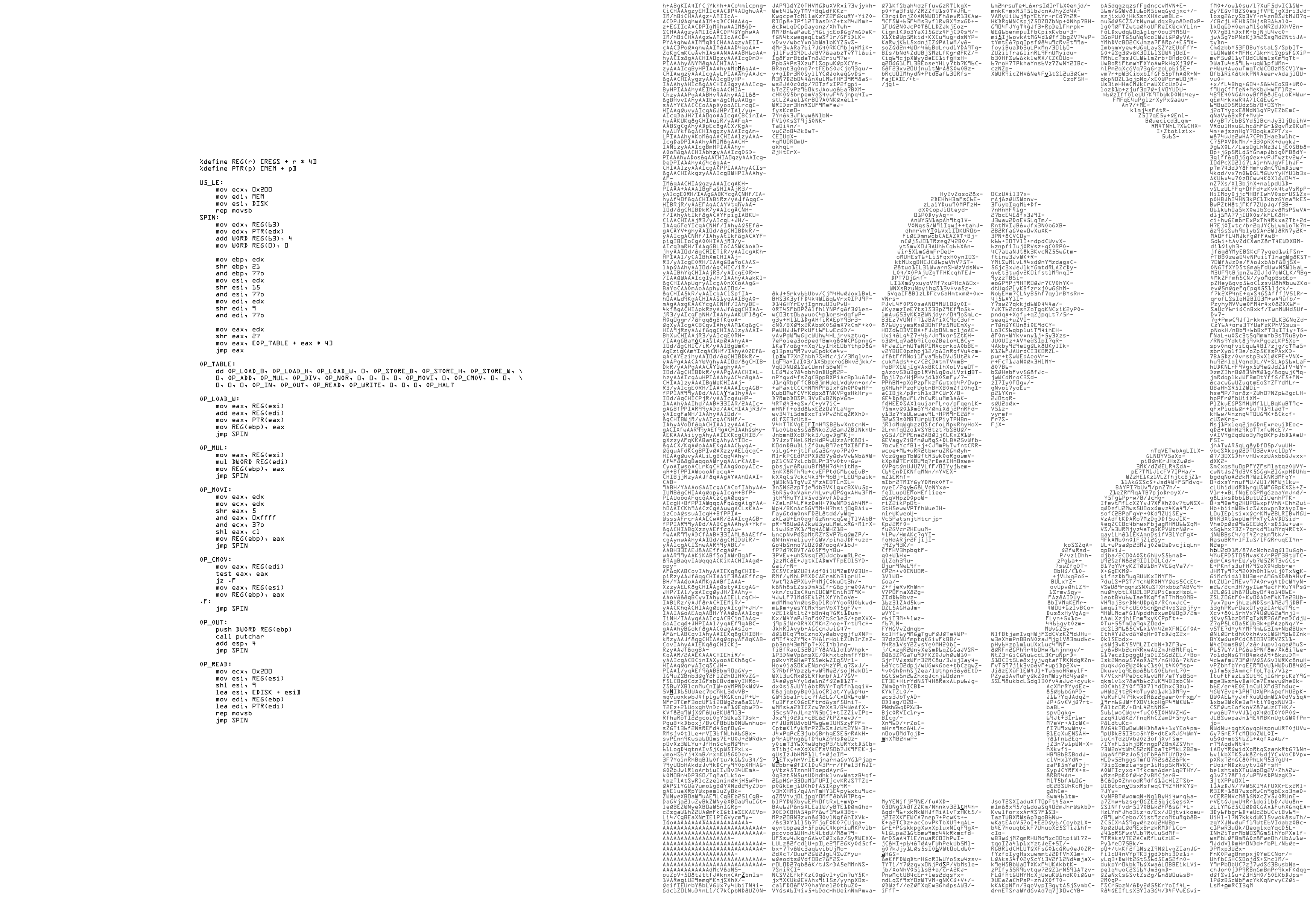
While I was browsing the Reverse Engineering sub on Reddit a few months ago, I came across a puzzle that the poster said came from a Danish newspaper.
It consisted of a single fairly large image, with a small amount of x86 assembly on one side, and a large block of text on the other, formatted to
display a question mark. So, having finally had the time to sit down and solve this recently, I thought I would do a writeup, explaining my
thought processes along the way in the hopes someone can learn from it. Another goal here is to expose people to the majesty of Radare2, which
is a Vim-like commandline reverse engineering tool that follows the principles of the Unix philosophy.
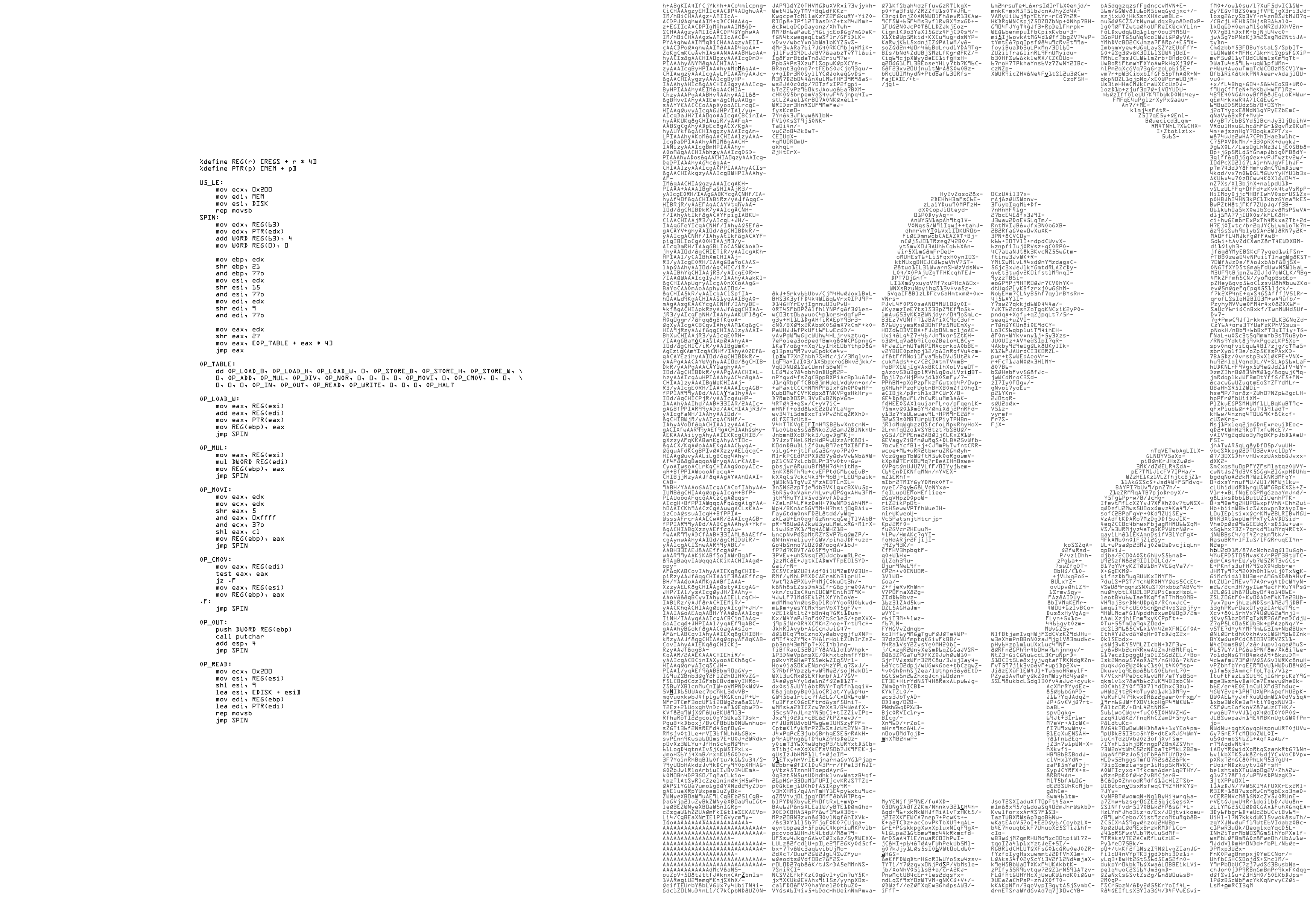
It looks like a CrackMe, or capture the flag exercise. The x86 assembly is clearly a virtual machine, and I assumed the block of text on the
right would be a binary that runs on that virtual machine. I call the machine, for lack of a better name, Dan32, because as I later
found out, it is a 32-bit virtual machine, and originates from Denmark.
The block of text on the right is base64 encoded, which is easy enough to to convert back into a binary file, but since it is an image,
we can’t directly get at that block in a text format without doing some kind of optical character recognition. We can guess it is base64
encoded by the characters used, and really after you’ve seen a lot of base64, you can usually spot it pretty easily.
I tried a few online OCR services, which did not work, and since I had invested almost no time into this, I was ready to say the hell with it.
I was not about to type all that base64 text into my text editor by hand.
I did end up solving this puzzle and creating tools to reverse engineer it, what follows is a detailed writeup, read on for more.
Note: If you are using a blocker such as Privacy Badger, like I do, I’ve noticed the terminal movie playback embeds from asciinema.org may
be blocked by default. If you wish to see those in this post, you’ll have to toggle that domain to allow in your plugin, though you don’t
need to accept cookies from that domain for it to work.